It is now possible to make dynamic row level security on a field in a semantic model.
With dynamic security you can read row level security dynamic from a table placed in a DWH or BU.
That table could be based on an excel file that is full loaded on execution, which makes this way of applying row level security dynamic.
Follow these steps to set it up.
1. Right click on a semantic field and select Add row level security.
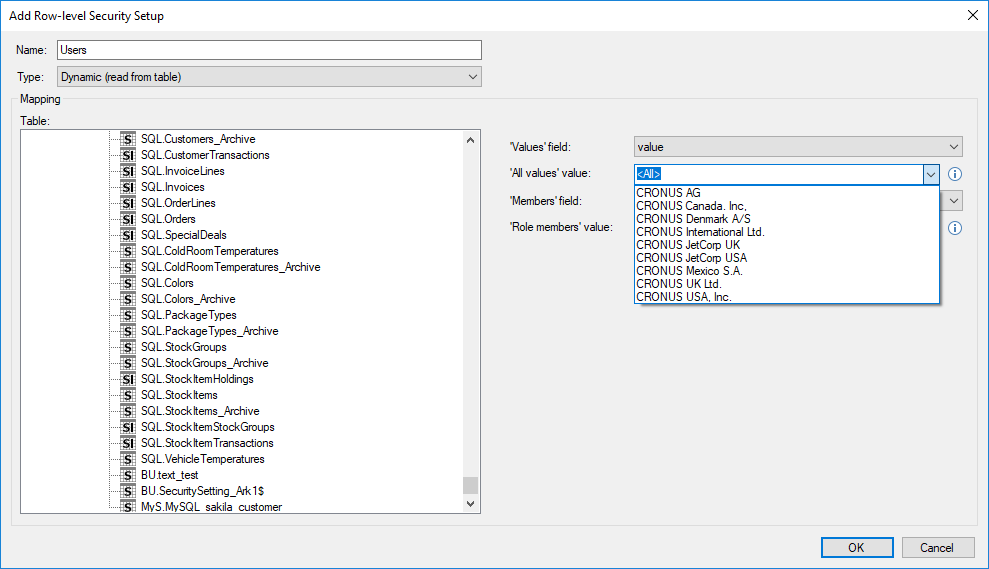
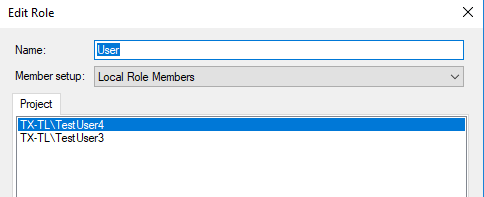
2. Change type to Dynamic (read from table)
3. Now select the security table to use for this field.
4. In the values field combo box select the column containing column data.
5. In the drop-down type or select the definition of ‘All values’. *
6. In the Members field combo box select the column containing role members.
7. In the drop-down type or select the definition of ‘Role members’. *
8. Press OK.
* So in manual security setup we have a definition for all values and all role members defined to <all> and (role members). Like this picture displays.
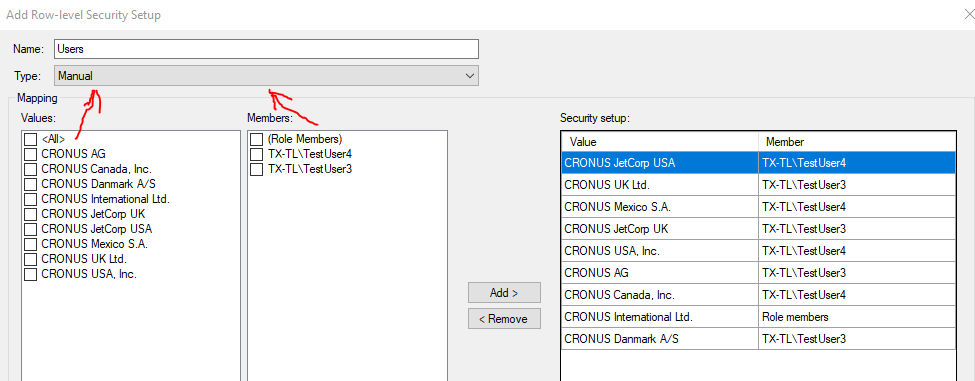
In dynamic security the user defines those values themselves.
In cases where your table don’t contain those values to select because you don’t have any cases where you map like that. Then you need to type in values you would consider using in the future as those definitions.
Example with file
Here is a quick example I have a excel file, that is set up, so I can get similar rights similar to the manual setup in the first image.
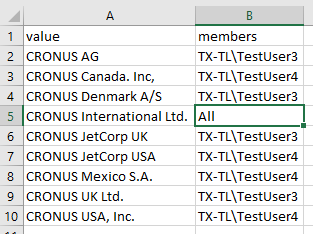
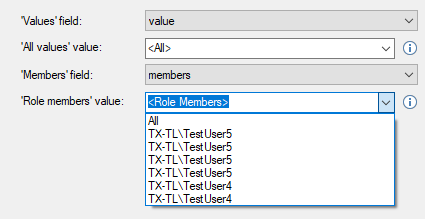
I use that as a data source and points to the excel data source. The Values field points to the value field in the table and the Members field points to the members field. I type <All> in the All values field, to point to all fields in the values.
I then type <Role Members> in the members field, or optionally I can point to the All value.
Now it is set up. The only thing to remember is that the Users setup needs to point to the User Role
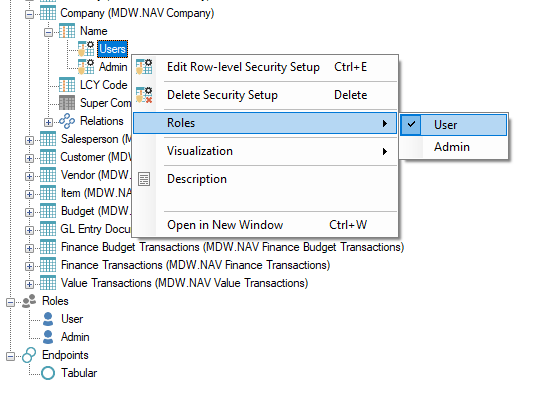
The User role needs to point at the Users setup
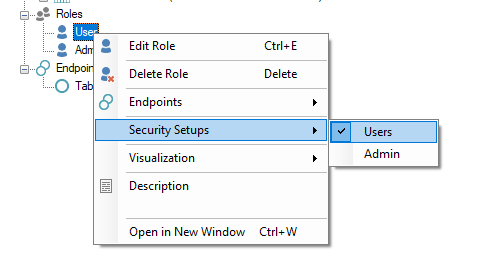
And the Role needs to contain the users you use in the setup.
0 Comments